Integrating NIST RMF, Clark-Wilson, and STRIDE to move beyond perimeter defense and secure the data lifecycle.
If the network is the castle wall, the database is the throne room. It is where the "crown jewels"—customer analytics, financial records, and proprietary algorithms—actually live. Yet, in our rush to secure the perimeter with firewalls and EDRs, we often leave the vault itself vulnerable to the very people who hold the keys.
The reality of modern breaches is stark: attackers don't just want access; they want data. Whether it’s state-sponsored espionage or ransomware gangs, the database is the final objective. Securing it requires more than just a strong password. It demands a multifaceted strategy that weaves together strategic governance (NIST RMF), formal integrity models (Clark-Wilson), and aggressive threat modeling (STRIDE).
1. Governance as the First Line of Defense
Data Classification & Prioritization
You cannot defend what you cannot define. The most common failure in database security is treating all data as equal. The NIST RMF's "categorize" step forces us to assess probable loss impacts. A public marketing database might survive with basic controls, but a HIPAA-regulated patient record requires a digital fortress. Classification isn't just paperwork; it is the blueprint that tells security engineers where to allocate their limited resources.
Killing "Privilege Creep"
The Principle of Least Privilege (PoLP) is often preached but rarely practiced. We rely on Role-Based Access Control (RBAC), but roles are static. People move, projects change, but access remains. This "privilege creep" creates ghost accounts that attackers love to exploit. The modern solution is Attribute-Based Access Control (ABAC)—context-aware enforcement that checks not just who you are, but where you are, what time it is, and the security posture of your device before granting access.
2. Technical Safeguards: Beyond the Firewall
Encryption: The Last Resort
When the perimeter fails—and it will—encryption ensures the loot is worthless. We must protect data in three states:
Database Activity Monitoring (DAM)
Logs are the black box of your database. Technical safeguards must include active detection. Database Activity Monitoring (DAM) tools don't just record queries; they flag anomalies. If an HR administrator suddenly exports 50,000 records at 3:00 AM, the system should trigger an alarm immediately—not next week during an audit.
3. Integrity by Design (The Clark-Wilson Model)
Confidentiality keeps data secret, but Integrity keeps it true. The Clark-Wilson model (1987) gave us the framework for preventing corruption, and it is more relevant today than ever for preventing ransomware tampering.
The critical data (e.g., bank balances) that must never be modified directly by a user.
The "Gatekeepers." Trusted code (like APIs) that validates every change before touching the CDI.
By forcing all changes through Transformation Procedures (TPs), we prevent direct tampering. In modern DevOps, your API layer acts as the TP—validating input, checking rights, and ensuring business logic is met before writing a single byte to disk.
4. Threat Modeling with STRIDE
We cannot rely on hope; we must anticipate attacks. Using Microsoft's STRIDE model, we can map out exactly where our database is exposed. The diagram below maps the critical data flows (D1 - D14) where we must apply controls.
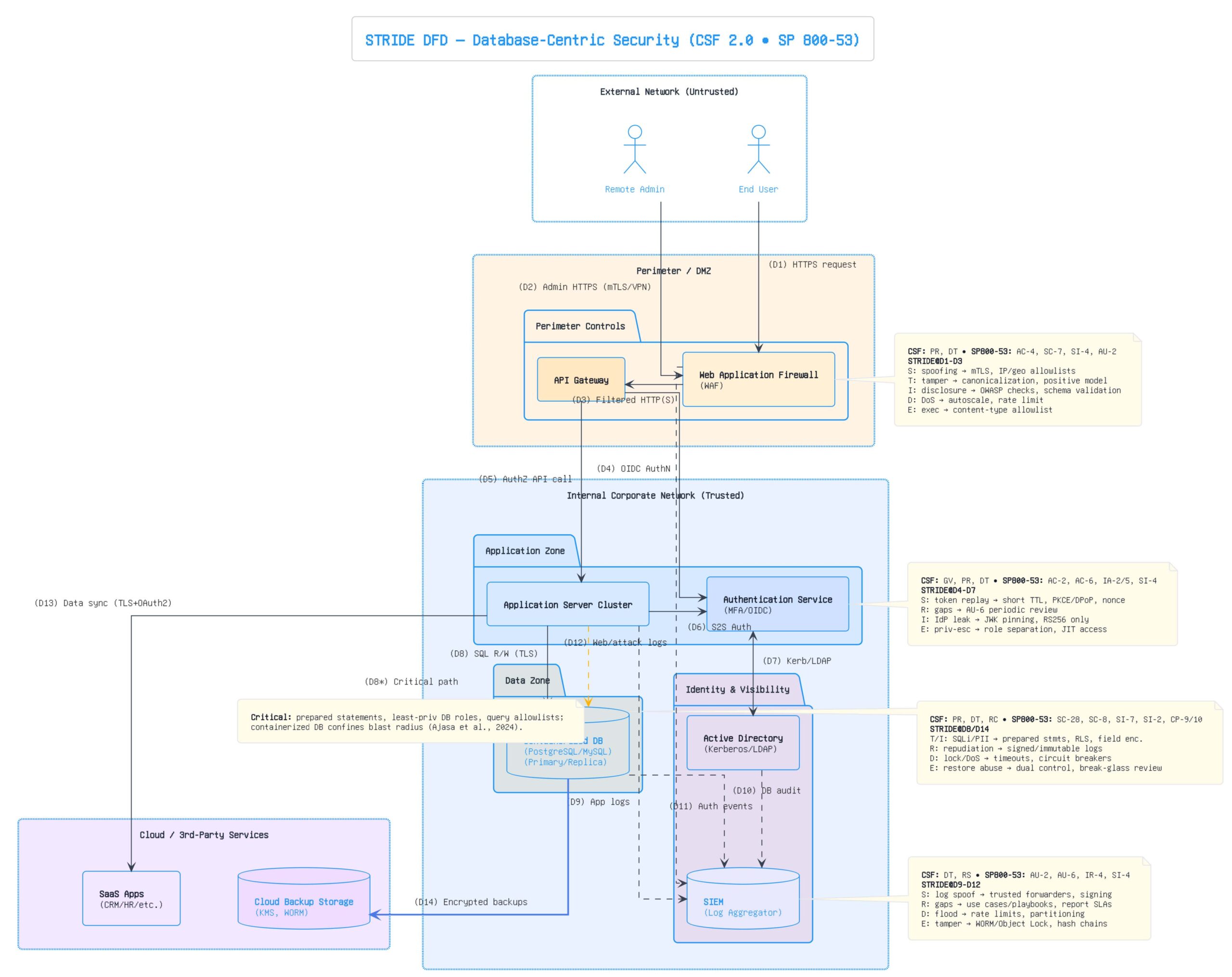
As shown above, the threat model identifies choke points. Spoofing dominates the perimeter (D1, D4), while SQL injection poses a threat to the application-to-database connection (D8). The matrix below outlines the specific mitigation strategies for each flow.
| STRIDE Category | Threat Scenario | Mitigation Strategy |
|---|---|---|
| Spoofing | Credential stuffing and phishing against admin portals. | Phishing-resistant MFA (FIDO2/WebAuthn) and IP reputation filters. |
| Tampering | SQL Injection modifying records. | Parameterized queries, ORM frameworks, and WAF signatures. |
| Repudiation | Shared "admin" accounts masking who did what. | Eliminate shared accounts; enforce immutable centralized logging. |
| Information Disclosure | Misconfigured cloud backups exposed to the public internet. | Encryption at rest (KMS) and strict IAM roles for backup buckets. |
The Future: Containerization & Zero Trust
The most vulnerable point in any system is the connection between the app and the database (Flow D8). Even with parameterized queries, risks exist.
Containerization offers a powerful defense. By isolating databases within Kubernetes pods and applying microsegmentation, we limit the blast radius. If a container is compromised, it can be destroyed and redeployed from an immutable image in seconds, effectively "healing" the breach before the attacker can pivot.
Conclusion
Database security is not a product you buy; it is a strategy you enforce. It requires a layered approach where Governance sets the rules, Technical Controls enforce them, and Threat Modeling constantly tests them.
As we move toward AI-driven analytics and quantum computing, the threats will only grow more sophisticated. The organizations that treat their data like a strategic vault—locking it from the inside out—will be the ones that survive.